Speech Pathology Application
| Sponsors | Micron Foundation |
| Team Name | Horsemen of the Epiglottis |
| Duration | 2018 - 2019 |
| Faculty Adviser |
|
| Client |
|
| Team Members |
|
The goal of this project is to build off of last year's Speech Therapy App, adding additional features such as a Database and GUI. This setup should allow for much easier access to child speech data. The database should allow the program to be easily expanded upon.
Problem Definition[edit | edit source]
This project is a continuation of a project from the 2017-2018 school year. In their project, they created the majority of the speech recognition processes with a basic GUI. The existing program provides prompts for users, and informs them of the phones that were not pronounced correctly. It also provides waveform and frequency visualizations of their speech patterns,which is less for the child and more for a therapist who would understand the diagrams. The program recognizes all English phones, and is based on a speech recognition library called Sphinx. The team’s duty for this year is to build off the last team’s work. Faced with a number of possible courses of action, they chose to build a better GUI and implement a database. As it is, the GUI is not exceptionally visually appealing, nor is it very child friendly. The intention is to retain the features of the program, but present them in different ways depending on who is using the program, the child or the therapist. The database, on the other hand, is a portion of the original project that just wasn’t obtainable within the timeframe given. With it, the team intends to provide an efficient way to store the children’s speech data, so that it is easy to find and sort. The team would also like to provide a way of creating a sort of “profiles” for the various children, making it easier for the therapist to switch between multiple patients.
Background[edit | edit source]
Around 1 in 12 children require speech therapy in the US. Our sponsor’s daughter began speech therapy, and soon after, he recognized the need for readily available speech therapy tools. This led Eric Booth and Ujjwal Roy to begin a project to do just that. Research has shown that the effectiveness of speech therapy directly correlates to the number of quality repetitions the participant does. They also found that, although many speech analysis tools exist, they are all lacking in the same way. They are not nearly as effective on children as they are on adults. In part, this is due to the unpredictable changes in children’s speech, but the main problem is the lack of data. Child speech is covered by numerous laws such as COPPA and HIPAA that make the collection and use of data difficult. This program can help people better understand what children with impediments are struggling with. The fact it is planned to be open source leads to even more possibilities. It provides the chance for communities of developers to alter it for use in other regions. On top of that, its convenience allows more time for children to work on their speech.
Deliverables[edit | edit source]
- Secure database that stores account information and vocal recordings
- Different User Accounts
- Therapist
- Care Giver
- Researcher
- Developer
- Ability to sort and display specific data sets
- Ability for researchers to submit speech data to the database
- Ability to port database to different services
Specifications[edit | edit source]
- Cloud based system
- Has set up the environment for our application
- Must have a 12 month free period
- Must scale easily
- Must be able to use and port to other services
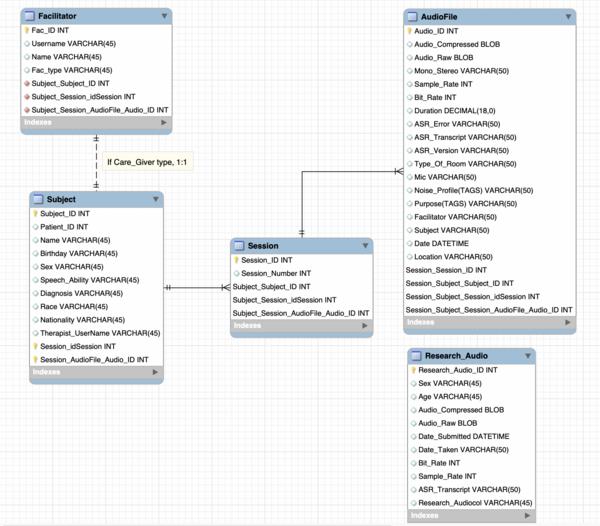
Database Diagram[edit | edit source]
Project Learning[edit | edit source]
Databases[edit | edit source]
- MySQL
- Open-source relational database management system (RDBMS)
- Using Structured Query Language (SQL)
- Small size, fast speed, low cost of ownership
- SQL: Grammar (CREATE TABLE my_table; to create a table)
- Functions (AVG (numericTerm),The average (mean) value.)
- Data Types (CHAR Type,A fixed length String)
Cloud Platforms[edit | edit source]
- Choices:
- Amazon Web Services (AWS)
- Google Cloud Platform (GCP)
- Microsoft Azure.
- Flexible: price, location, time, and cloud configuration
- Provide many related service for our chosen product (security, and disaster recovery for cloud database product)
- The cloud provides multiple layers of security including, but not limited to data communication encryption, identity management, and threat detection.
Security[edit | edit source]
- One of the primary concerns with this project is conforming to laws such as COPPA and HIPPA, meaning that security is a necessity. This team is examining a number of different methods of maintaining the security of the database.
- Backups
- “Regular backups protect against the risk of damage or loss due to hardware failure, software or media faults, viruses or hacking, power failure, or even human errors.” -https://www.library.cmu.edu/datapub/dms/data/secure
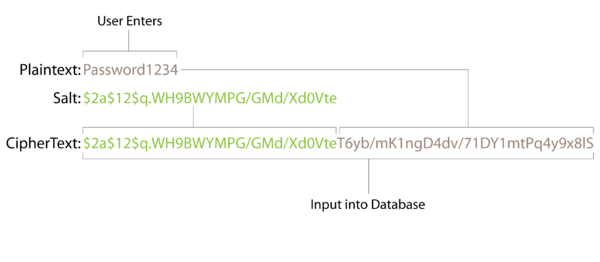
- Password hashing
- Encryption is two way, so less safe
- Hashing is a one way function and therefore more secure
- The figure below shows the general structure of hashing passwords for the database
- Privacy level accesses
- Certain facilitator types can only access a subset of information.
- Hashing Algorithms
- Normal algorithms like SHA and MD5 are good, but are actually too efficient, leading us to seek a different algorithm
- Ended up settling on an algorithm called BCrypt
- BCrypt is viewed as a standard as far as password hashing algorithms go
- Allows the users to decide how many times the algorithm will be run on a password, changing the runtime of the function.
Team Members[edit | edit source]
| Hailey Johnson
Major: CE | |
| Wei Zhao
Major: CS
| |
| Jordan Cates
Major: CS
|
Additional Documentation[edit | edit source]
Project Schedule
Meeting Minutes
9-14-18
9-26-18
9-28-18
10-1-18
10-2-18
10-3-18
10-12-18
10-15-18
10-19-18
10-24-18
10-26-18
11-2-18
11-7-18
11-9-18
11-26-18
11-30-18
12-7-18
1-28-19
2-12-19
2-27-19
Presentations